Today, I am pleased to share a new white paper about cybersecurity norms for nation-states and the global information and communications technology (ICT) industry, “From Articulation to Implementation: Enabling Progress on Cybersecurity Norms.” This publication is a reflection of our ongoing efforts to advance trust in the global ICT ecosystem through development of “rules of the road” for nation-states engaged in cyber operations, as well as industry actors impacted by these activities. Our goal is to contribute to the development of frameworks and practices that protect people and companies from the effects of state-sponsored cyber operations.
Global ICT companies acutely understand that technology products and online services, including the underlying internet infrastructure, are often the battlefield for cyber conflicts and conduit for other attacks launched by governments and their proxies. (Learn more about our views on government activity online as a cyber threat category.) Because of this phenomena, Microsoft believes that cybersecurity norms are not just for governments, and the global ICT industry must also undertake commitments that enhance trust in ICT systems. This perspective is reinforced by the United Nations Group of Governmental Experts, an intergovernmental task force charged with developing cybersecurity norms, which called upon the private sector and civil society to contribute to the development of cybersecurity norms.
In our new paper, we put forward a three-part organizing framework for the current cybersecurity norms dialogue: offensive norms, defensive norms and industry norms. Offensive norms are the province of nation-states, as these norms concern self-restraint in the conduct of cyber operations. Defensive norms are relevant to both governmental and non-governmental actors because these norms address defensive measures against nation-state activities in cyberspace. Industry norms are also important to both governments and the private sector, but are focused on addressing industry’s role in mitigating the risks facing technology users from nation-state activity in cyberspace.
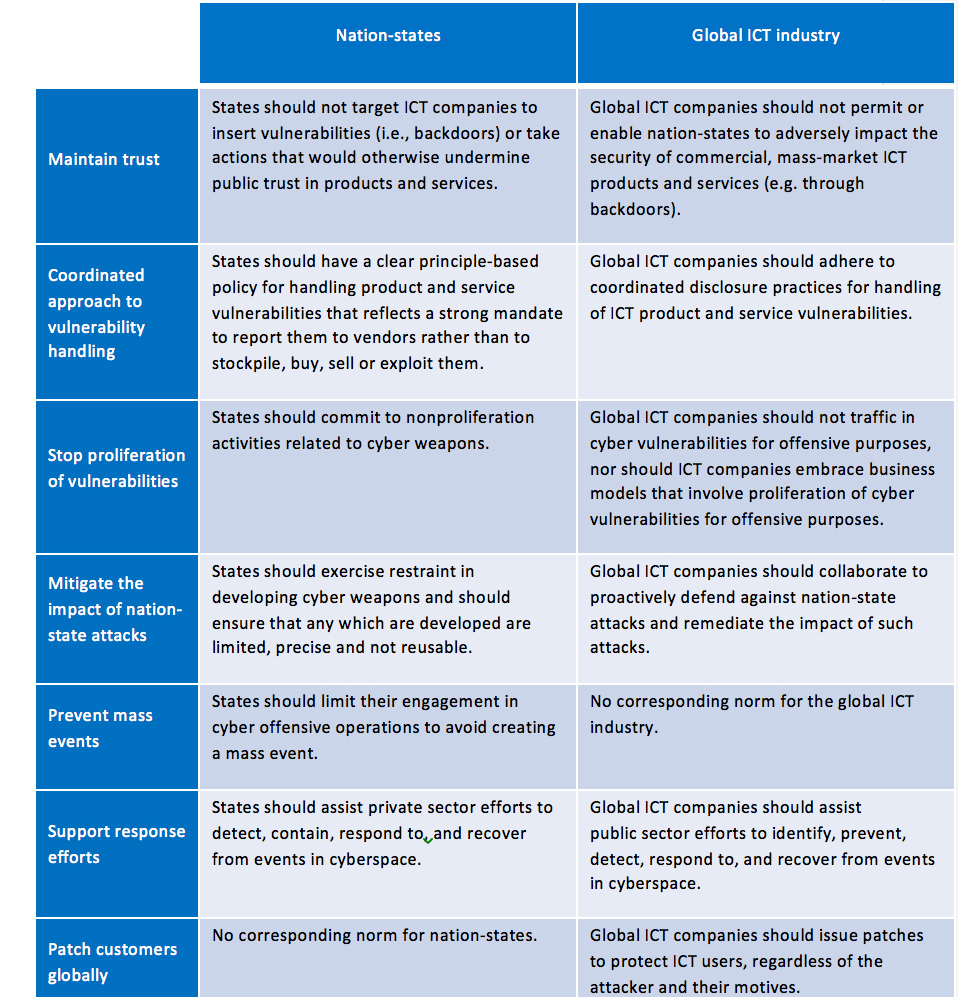
We believe that norms should advance common objectives where possible, regardless of whether the norms are focused on offense, defense or industry. The chart below provides a side-by-side view of Microsoft’s proposed norms for nation-states, with our corresponding proposals for industry norms. While there is a strong complementary structure for nation-state norms and industry norms, they vary in two important instances: nation-states possess the ability to create mass effects through offensive cyber activities; and the global ICT industry has the ability to patch all customers, even during conflicts between and among governments. (Learn more about our proposed norms for nation-states.)
We recognize that cybersecurity norms are unlikely to be effective as a policy tool without further development of cyber attack attribution processes. Accordingly, our paper outlines the current challenges surrounding attribution of cyber attacks, and we propose a public-private forum to address attribution of severe cyber attacks that would involve a globally-diverse group of technical experts, subject to peer review. Indeed, the development of cybersecurity norms will require new forms of cooperation and new mechanisms to surmount challenges that are unique to cyberspace. New models for public-private partnership – on a global scale – will be essential.
As governments commit increasing resources into offensive cyber capabilities, the global ICT industry must strengthen its resolve, and take active steps to prevent user exploitation through adherence to industry norms. We must continue to raise the bar in our defensive capabilities to deter nation-states from targeting technology users. We hope these proposed norms set government and industry on a path for broader discussions to enhance trust between governments, enterprises and technology users.