<p>A vulnerability disclosure, as the term is used in the <a href="http://www.microsoft.com/sir">Microsoft Security Intelligence Report</a>, is the revelation of a software vulnerability to the public at large. Disclosures can come from a variety of sources, including publishers of the affected software, security software vendors, independent security researchers, and even malware creators.</p>
<p>The vulnerability disclosure data in the Security Intelligence Report is compiled from vulnerability disclosure data that is published in the <a href="http://nvd.nist.gov/">National Vulnerability Database </a>(NVD). This database is the US government’s repository of standards-based vulnerability management data. The NVD represents all disclosures that have a published Common Vulnerabilities and Exposures (CVE) identifier.</p>
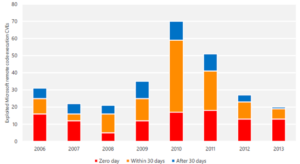
<p><span style="text-decoration:underline;"><strong>Industry-wide vulnerability disclosures trending upwards</strong></span><br>Figure 1 illustrates the vulnerability disclosure trend across the entire industry since 2011. Between 2011 and the end of 2013 vulnerability disclosure counts ranged from a low of 1,926 in the second half of 2011 to a high of 2,588 in the first half of 2012; there were more than 4,000 vulnerability disclosures across the entire industry each year during this period. For <a href="/b/security/archive/2012/03/15/trustworthy-computing-learning-about-threats-for-over-10-years-part-4.aspx">additional context</a>, the peak period for industrywide vulnerability disclosures was 2006-2007 when 6,000 - 7,000 vulnerabilities were disclosed each year. Vulnerability disclosures across the industry in the second half of 2013 (2H13) were up 6.5 percent from the first half of the year, and up 12.6 percent from the second half of 2012. <a href="/b/security/archive/2014/07/08/industry-vulnerability-disclosures-trending-up.aspx">Read more</a></p>